1 Introduction
After the M1 card was cracked in the laboratory, the official Chinese government has used the crack algorithm to reproduce the cracking process of the Ml card. The whole process is completed within 10 seconds. The relevant domestic authorities have officially issued a document at the end of February 2009. Based on the security crisis of the M1 card, all the card application units are required to fully understand the grim situation of this incident, and the corresponding countermeasures should be taken in the first time to realize the M1 card to the CPU card. Smooth, smooth transition.
The CPU card is a contactless IC card, which has a central processing unit CPU, EEPROM, random access RAM, and an on-chip operating system COS (Chip Operating Systerm) that is solidified in a read-only memory ROM. On the other hand, the security is greatly enhanced. It also increases the flexibility of card application expansion.
The 1+N model is a data model that is portable, easy to expand, hierarchical, and centralized in management for the high openness and high integration requirements of the card system. The 1+N model is characterized by software as the core, which realizes the separation of software and hardware, thus achieving centralized storage, unified management, unified service authorization, and flexible access of devices and subsystems.
At present, the construction of the card system generally has problems such as poor openness of the platform, unfavorable development of card application, disorderly construction of the card project, and limited improvement of enterprise management. This paper proposes a card platform combining CPU card technology and 1+N model. The design plan, firstly, expounds the key technologies involved in the system, and then proposes a design plan for the special functions in the civil aviation field. Finally, taking the application at Shenzhen Baoan International Airport as an example, it proves that based on CPU card technology and 1+N The card system of the model can effectively solve the problems existing in the construction of the current card system and improve the security of the system.
2. Key technologies
2.1 Contactless CPU Card Technology
The CPU card is a card with a central processing unit CPU, EEPROM, RAM, and in-card operating system COS. It is a true smart card, which is often referred to as a SmartCard. CPU card integration includes the central processing unit (CPU), read-only memory (ROM), random access memory (RAM), EEPROM and other major parts, with the card operating system COS (Chip Oper-ating System), with COS to achieve Card data protection, such as user and system mutual authentication, application sequence control and management, random number generation and transmission, key management, encryption, decryption, secure transmission of information, etc., the structure of the CPU card is shown in Figure l . Source card world. The CPU card is like an ultra-small computer. It has the advantages of large amount of information, high security against anti-counterfeiting, offline operation, and multi-functional development. Compared with the logical encryption card, the CPU card has an independent CPU processor and chip operating system, so it can more flexibly support various application requirements and design the transaction flow more securely.
The ROM is used to store the operating system (COS) on the CPU card, read data from it when the system starts up, load the operating system, and manage the computer on the entire card. The RAM is used to store the intermediate processing results of the system and acts as an intermediate buffer for information exchange between the card and the reader. CPU cards usually use encryption/decryption algorithms such as DES and RSA to improve the security performance of the system. These security algorithms require a lot of mathematical operations, and 8-bit CPUs will be difficult to undertake complex mathematical operations. Therefore, many CPU cards are specifically designed for use in CPU cards. Coprocessor CAU for encryption/decryption operations. The EEPROM is a storage area accessed by the user for storing various information, passwords, keys, application files, and the like of the card. The external read/write device can only exchange data with the EEPROM in the card through the CPU. Under no circumstances can it directly access any data in the EEPROM. When the external read/write device exchanges data with the CPU card, it must first issue a command to the CPU of the card. The CPU interprets the command according to the card operating system (COS) stored in the ROM, and analyzes and judges the device. After the legitimacy, the external read/write device is allowed to establish a connection with the card. After the data operation, the external read/write device still issues corresponding instructions, and the CPU interprets the instruction correctly, allowing the external read/write device and the card to be randomly stored. The area (RAM) exchanges data. After the data exchange is successful, under the control of the CPU, the internal data bus of the card is used, and the data in the RAM is exchanged with the data in the EEPROM. This achieves the security protection of the data in the EEPROM.
2.2 1+N architecture model
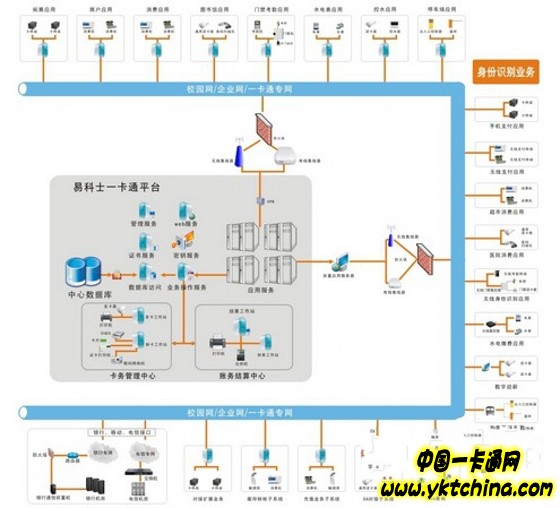
The lowest level system platform and application platform form a card platform. The card platform is basically fixed, which is equivalent to the "1" part of the model. The upper management platform, application system and various interfaces are added on the basis of the platform according to requirements. It is a relatively flexible part, which is the "N" part of the model. The card platform consists of a front-end platform, a WEB service platform, a data center, a cluster, and a database. The front-end platform is an intermediate device between the platform and the application to solve cross-system communication problems. It has a very powerful function, and it can be Transaction data format conversion, dynamic key update, transaction message authentication and personal password PIN conversion, transaction monitoring, data collection and replenishment, flow recording and data statistics, and start-up instructions, front-end device management The clock of the front-end device is synchronized, and the blacklist management is responsible for realizing the management of the POS machine. The WEB platform provides a data access mechanism in the B/S mode. Data centers, clusters, and databases enable centralized deployment of the entire system database.
3. Design and implementation
3.1 System Architecture
The card system is assigned a separate VLAN, and the card data center communicates with each subsystem and terminal device through the TCP/IP protocol. The system deploys three clients: the card management client, the accounting management client, and the system management client. All client software is connected to the same database, and the system implements “data concentration and information sharingâ€. The authority of each system operator is granted by the system administrator to achieve "centralized management" of the operator privileges of the card system. The same set of management software is installed on each management workstation. Each operator login system is a system that is selected according to its own authority. It is not necessary to install the client software separately for each application module to achieve "distributed control".
Fruit Basket,Fruit Hamper,Apple Basket,The Fruit Basket
Jiangmen Sunbond Houseware Manufacturing CO.,LTD , https://www.sunbondhw.com